Russian Cybercrime Group, Clop, Threatens to Publish Stolen Data in Global Hack
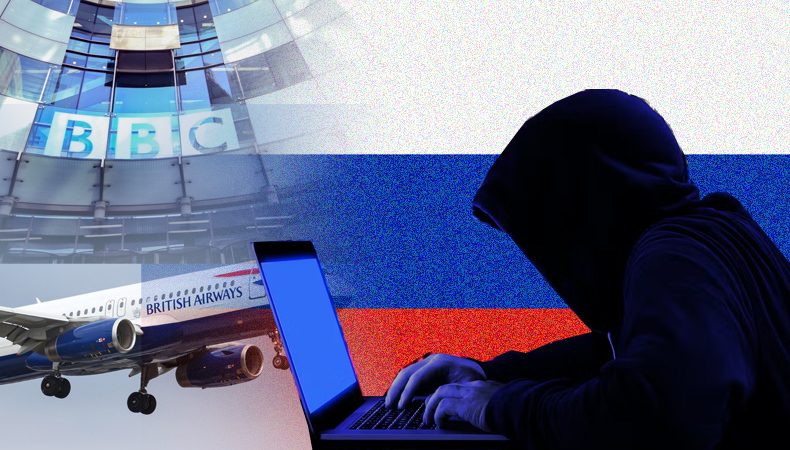
A notorious cybercrime gang believed to be operating out of Russia, known as Clop, has issued an ultimatum to victims of a recent global hack. The group has posted a notice on the dark web, warning organizations affected by the MOVEit hack to contact them before June 14th, or risk having their stolen data publicly released. The hack has impacted prominent entities such as the BBC, British Airways, and Boots, potentially compromising the payroll data of over 100,000 employees. Despite the ransom demands, cybersecurity experts advise affected organizations against paying and instead recommend implementing security checks provided by relevant authorities.
Also Read – 4 reasons you need to invest in a technology upgrade for your business
The MOVEit Hack and Clop’s Ultimatum
Clop’s modus operandi involves infiltrating a widely-used business software called MOVEit, subsequently exploiting this access to breach the databases of numerous other companies. Analysts from Microsoft, who initially suspected Clop’s involvement, have now confirmed it through a blog post written in broken English. The post aims to educate affected companies about the large-scale data breach and urges them to initiate negotiations by emailing the cybercriminal gang via their darknet portal. It is noteworthy that Clop is demanding contact from the victims, a departure from the typical approach where ransom demands are directly emailed to targeted organizations. This deviation suggests that Clop might be struggling to manage the vast scale of the ongoing hack.
The Impact of the MOVEit Hack
MOVEit, a software provided by US-based Progress Software, facilitates secure file transfers within organizational systems and is extensively used by businesses. Among its users, the UK-based payroll services provider Zellis confirms that eight organizations, including the BBC, British Airways, and Boots, have had their data stolen. The stolen information includes home addresses, national insurance numbers, and, in some cases, bank details. It is important to note that not all firms experienced the same data exposure. To address the situation, experts advise individuals not to panic while recommending that affected organizations perform security checks issued by relevant authorities such as the US Cyber Security and Infrastructure Security Agency.
Clop’s Claims and Trustworthiness
On its leak site, Clop asserts that it has deleted data related to government, city, or police services, stating, “Do not worry, we erased your data, you do not need to contact us. We have no interest in exposing such information.” However, cybersecurity researchers caution against trusting the criminals’ claims. Brett Callow, a threat researcher from Emsisoft, states that Clop’s assurance of deleting information concerning public sector organizations should be taken with skepticism. If the stolen information holds monetary value or can be exploited for phishing attacks, it is unlikely that the hackers have truly disposed of it. Thus, organizations and individuals should remain vigilant.
Clop’s Persistence and Global Response
Clop has long been on the radar of cybersecurity experts, who primarily associate the group with operations on Russian-speaking forums, suggesting a Russian base of operations. Although Russia denies providing safe havens to ransomware gangs, Clop operates as a “ransomware as a service” group, allowing hackers to rent their tools for attacks from any location. In 2021, Ukrainian, US, and South Korean authorities jointly apprehended alleged Clop hackers, leading to claims of dismantling the group responsible for extorting $500 million globally. However, Clop has resurfaced as an ongoing threat, demonstrating its persistence and ability to continue launching cyberattacks.
Also Read – Top Technology Companies to Work for in 2023
The cybercrime gang Clop, believed to be based in Russia, has issued a stark ultimatum to victims of the MOVEit hack, demanding contact before a specified date, or risk having their stolen data made public. Prominent organizations, including the BBC, British Airways, and Boots, have potentially had their payroll data compromised. In response, cybersecurity experts advise against complying with ransom demands and recommend following security checks provided by relevant authorities. Despite claims by Clop that they have deleted certain information, experts warn against trusting the criminals. Clop’s resilience underscores the ongoing challenges posed by cybercriminals, necessitating constant vigilance and robust security measures.




